165. Bjarne Stroustrup’s talks on safety, WG21 August mailing, Rust
With Gianluca Delfino, Frances Buontempo, Vladimír Arnošt, Ivor Hewitt et al.
Media
Video
Podcast
Powered by RedCircle
Life advice from Bjarne Stroustrup
- Don’t overspecialise
- Have a life and interests outside computing
- Build a portfolio of skills
- Be ready for the opportunity and don’t let it go unnoticed
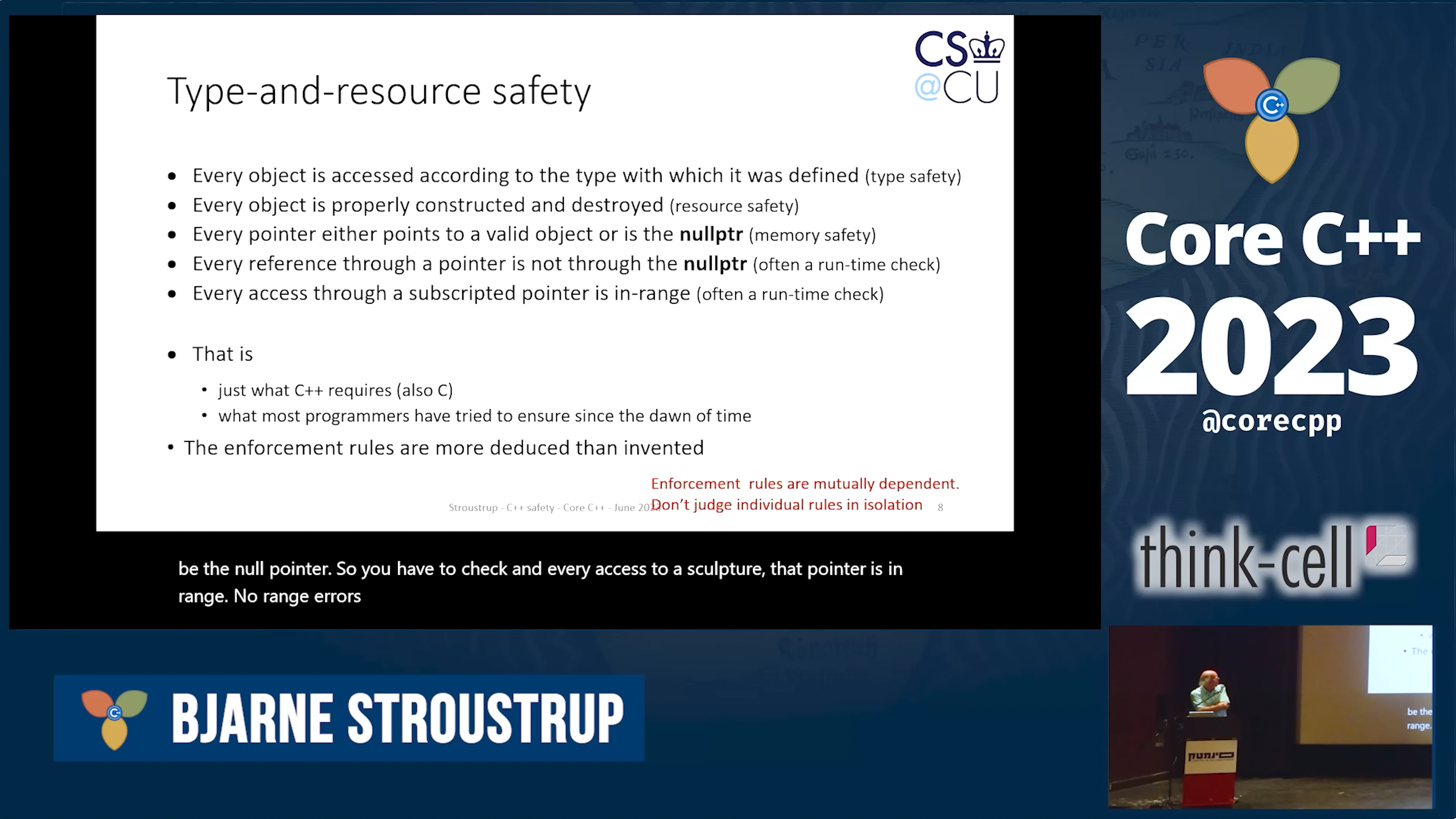
Approaching C++ safety - Bjarne Stroustrup (CoreCppIL 2023)
- Goal: type- and resource-safe C++
- The spooks (NSA) say don’t use C/C++ as it’s unsafe. I sort of agree, I don’t like C/C++, it’s a mythical language which is usually a mess.
- People choose C++ for a reason. The alternatives are new and shiny, but largely untried, and don’t handle the range of applications that C++ does.
- You just have to be careful, but being careful is not good enough.
- We can’t just "outsource" unsafe parts to another language.
- "RAII – Resource Acquisition Is Initialization – must be the dumbest name for a great feature. Apologies for that. I was busy."
- People come and say: "C++ is too complex, I want you to simplify it. By the way, while you’re at it, I want these two features added, I need them yesterday. And whatever you do, don’t break my code!"
- Safety by subsetting the language doesn’t work because lots of the low-level features aren’t safe.
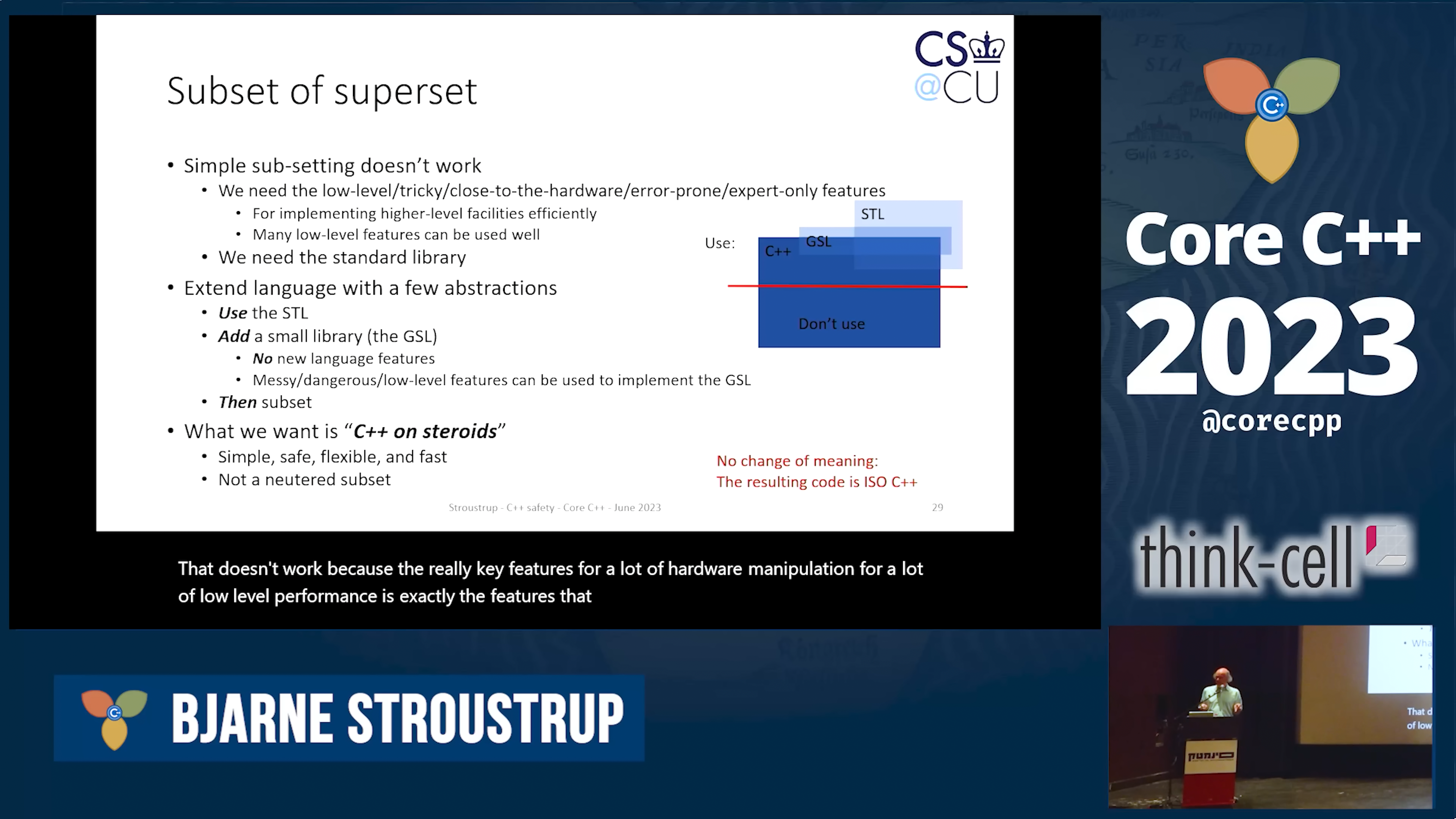
- Superset the language with libraries (STL, GSL) and then subset it.
- Different domains have different definition of "safety", but basic type and resource safety should be common.
- Arbitrary C++ code is simply too complex for static analysis.
- Profile: a coherent set of rules yielding a guarantee: bounds, type, memory etc. Must be visible in code (to indicate intent and to trigger analysis). Similar to Ada’s safety profiles.
- The hardest problem is mixing profiles.
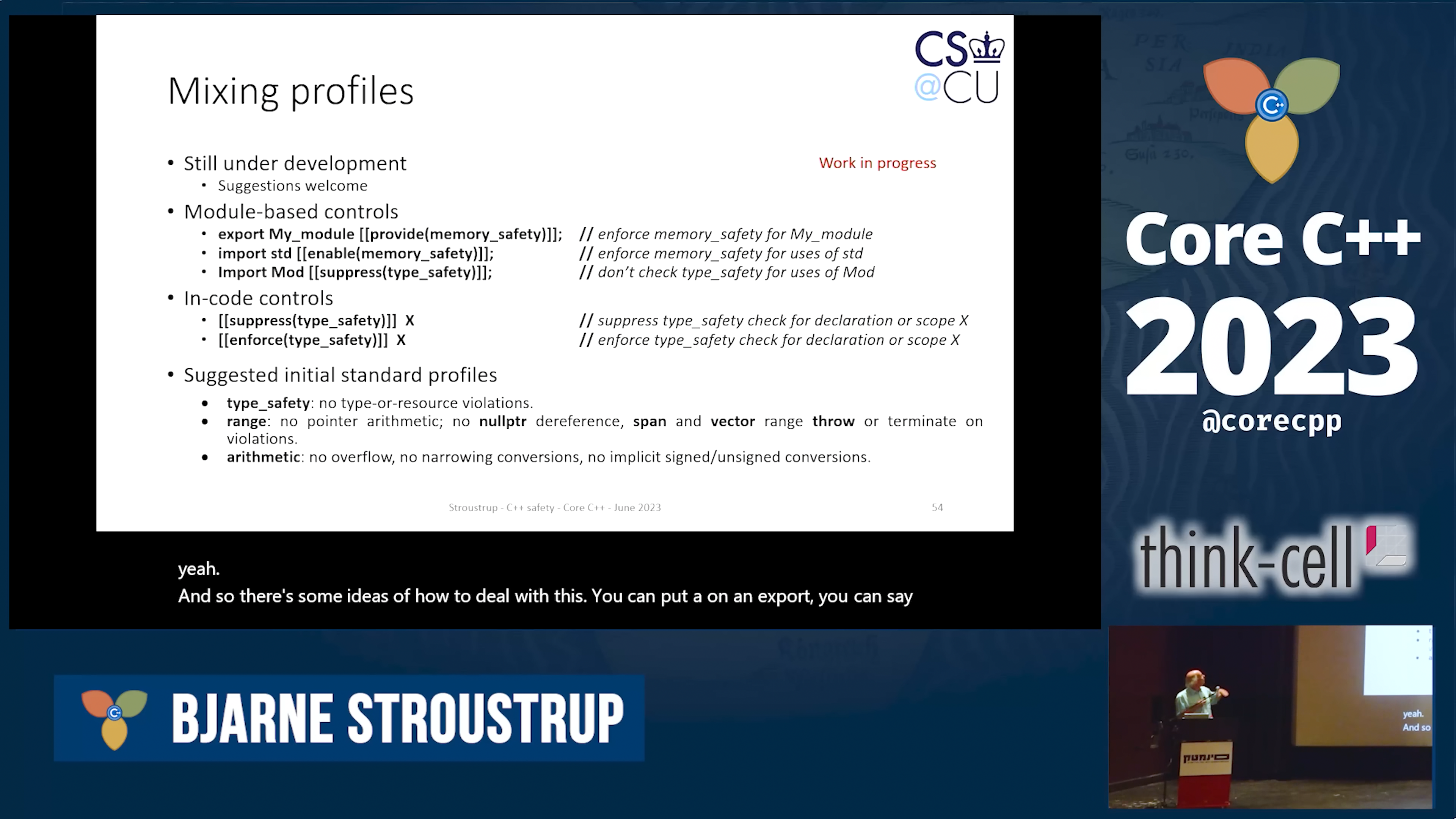
- Suggested initial profiles:
type_safety,range,arithmetic.
Hardening C++ (Bjarne Stroustrup, Software Engineering Daily, March 2023)
Don’t use "C/C++" but "try this other language which is not even standardized and has no formal definition, but it’s safe!" — give me a break!
WG21 Mailing, August 2023
Erroneous behaviour for uninitialized reads
P2795R3 by Thomas Köppe
We propose to address the safety problems of reading a default-initialized automatic variable (an “uninitialized read”) by adding a novel kind of behaviour for C++. This new behaviour, called erroneous behaviour, allows us to formally speak about “buggy” (or “incorrect”) code, that is, code that does not mean what it should mean (in a sense we will discuss). This behaviour is both “wrong” in the sense of indicating a programming bug, and also well-defined in the sense of not posing a safety risk.
We propose to change the semantics of reading an uninitialized variable:
Default-initialization of an automatic variable initializes the variable with a fixed value defined by the implementation; however, reading that value is a conceptual error. Implementations are allowed and encouraged to diagnose this error, but they are also allowed to ignore the error and treat the read as valid. Additionally, an opt-out mechanism (in the form of an attribute on a variable definition) is provided to restore the previous behaviour.
<…>
In other words, it is still an "wrong" to read an uninitialized value, but if you do read it and the implementation does not otherwise stop you, you get some specific value.
This paper seems like an opposite of the paper P2723 Zero-initialize objects of automatic storage duration. It looks like you can’t have both.
span.at()
P2821R4 by Jarrad J. Waterloo
This paper proposes the standard adds the
atmethod tostd::spanclass in order to address safety, consistency and PR (public relations) concerns. <…> If <index> is not within the range of the container, an exception of typestd::out_of_rangeis thrown.
An Attribute-Like Syntax for Contracts
P2935R0 by Joshua Berne
int f(const int x, int y)
[[ pre : y > 0 ]]
[[ post : fstate() == x ]] // Parameters referenced in post must be const.
[[ post r : r > x ]] // Postcondition may optionally name return value.
[[ post (r) : r > y ]] // Return value may have parenthesis.
{
[[ assert : x > 0 ]];
return x;
}Safer Range Access
P2955R0 by Jarrad J. Waterloo
Annotations!
Reference checking
P2878R5 by Jarrad J. Waterloo
More annotations!
This paper proposes that we allow programmers to provide explicit lifetime dependence information to the compiler for the following reasons:
- Standardize the documentation of lifetimes of API(s) for developers
- Standardize the specification of lifetimes for proposals
- Greatly reduce the dangling of the stack for references
What is being asked for is similar to but not exactly like Rust’s feature called explicit lifetimes.
Considering C++ over Rust
You can’t just place a
LISPRust book on top of an x86 chip and hope that the hardware learns about lambda calculus by osmosis.
Dave Plummer’s stupid C++ tricks
YouTube: https://youtu.be/p-sprvJX07E
Modern C++, not that vintage "orthodox" stuff!
Great anecdotes from the old days of Microsoft and Windows, like this one: at Microsoft they never called BSOD a blue screen of death – only blue screen, or a bugcheck, as it was initiated by calling the kernel function KeBugCheck.
Node.js is moving to a new, faster URL parser called Ada written in modern C++
Putting aside the confusing name which suggests the author didn’t know (or didn’t care) about the Ada language…
#define ADA_ROUNDUP_N(a, n) (((a) + ((n)-1)) & ~((n)-1))
#define ADA_ROUNDDOWN_N(a, n) ((a) & ~((n)-1))C++ in Chromium
Yeees, "Modern". <facepalm>
Why Rust will replace C++ in the future
This sounds to me like something written by ChatGPT. The irony is that the article was probably generated by code written in C++.
C/C++: well, actually
Predrag Gruevski writes on Mastodon:
Including C/C++ on my resume has been a great way of selecting out people that would be the kind of "well, actually" that I don’t think I’d enjoy working with.
Mastodon: pragma once
By aki-nyan:
if
#pragma onceis so good where is#pragma twice
Mastodon: clocks
A broken clock fixed by taping a working clock over it is a metaphor for every codebase you’ll encounter in your professional career as a software developer.